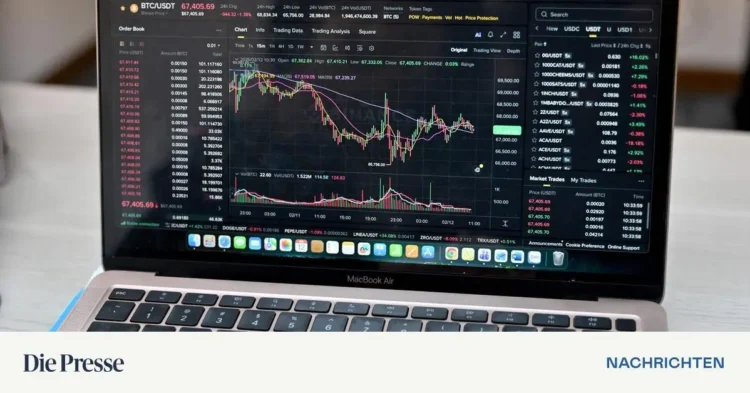
Vienna. A perpetrator blackmails someone, generates a Bitcoin address and asks his victim to transfer money there. Nobody knows who owns this Bitcoin address. And once the digital money has arrived there, no one can confiscate it unless they have the associated “private key”. Bitcoin, critics say, would be extremely suitable for crime. In fact, in several high-profile extortion cases in the past, the perpetrators demanded that the ransom be paid in cryptocurrencies. But how anonymous is Bitcoin actually?
Although Bitcoin addresses cannot always be immediately assigned to a specific person, they are not anonymous, but only pseudonymous. Everyone can view them, everyone can see how many Bitcoin are there, everyone can track where they go. Once the owner is identified at just one point, the entire transaction history can be linked to him. People are often identified when they try to exchange Bitcoin for euros or dollars on a regulated crypto exchange. In addition, everything that happens on the blockchain is stored there forever. Even if you get away with a crime once, that doesn’t mean you’ll stay that way forever. But unlike bank accounts, Bitcoin addresses cannot be frozen. However, authorities can prohibit regulated service providers from accepting these payments.
Nope. The more trading goes back and forth, the more difficult it becomes to determine which of the many new Bitcoin addresses still belong to the original owner. However, it can still be determined what proportion of an address’s inventory originally comes from the criminal transaction. Investigators are also trying to use analysis tools to determine the probability of which addresses still belong to the perpetrator and which do not. If you have the right knowledge, you can outsmart these tools. Depending on the severity of the crime, you also have to expect great persistence on the part of the investigators, whose analysis software is also getting better and better.
For example, with chain hopping (quickly swapping back and forth from one cryptocurrency to another) and the use of unregulated or decentralized platforms (DEX) where you don’t have to identify yourself. The cryptocurrency Monero, for example, has a reputation for offering a high degree of anonymity. Some criminals also use the services of large digital mixers to cover their tracks. The biggest problem for criminals is always the payout. Some use crypto debit cards (this process has recently become more difficult in the EU as card providers now also have to meet strict KYC requirements), informal underground systems, identity fraud, etc. Ultimately, it is a race between ever better cover-up tools and ever better investigative tools.
Theoretically yes, but at some point the criminals make mistakes. The Bitfinex hack is a prime example: In 2016, two hackers managed to hack the Bitfinex exchange and steal 120,000 Bitcoin. At that time they had an equivalent value of 60 million euros, today it would be almost eight billion euros. The perpetrators tried everything possible: they exchanged their loot for other cryptocurrencies several times, used numerous platforms, chased the money through digital mixers, and purchased gift cards and gold coins. Nevertheless, they made mistakes that led the investigators on their trail when they gained access to the servers of the darknet trading platform Alphabay: It turned out that the perpetrators had not clearly separated their criminal and private wallets. This made it possible to establish connections to accounts that were linked to the hackers’ real identities. The perpetrators also attempted to redeem Walmart vouchers using an email address that could be linked to them. To access their money laundering accounts, they did not use VPN or Tor, but the same IP addresses as for their private logins. During a house search, the investigators gained access to a cloud storage account, where they discovered the access keys (private keys) for the associated Bitcoins.
No, no one has managed to do that yet. Even normal users don’t have to worry. However, if you do not keep your Bitcoin access data (private keys or seed words) safe, they can be taken away or stolen. You should therefore never save them online, but only on a cold wallet (that is not connected to the Internet), or write them down (stamp them into steel plates) and keep them as distributed as possible.
Depends on. If you really only care about privacy, i.e. about not everyone being able to see what you spend your Bitcoin on, you can achieve a relatively high level of privacy by using Coinjoins or Lightning. A coinjoin bundles multiple payments into a single large transaction, and each participant receives a new payment. Coinjoins are less suitable for money laundering for criminal purposes because they are very time-consuming for large sums and require precise separation of wallets. And anyone who merges the money they receive from a coin join with the holdings from a known address (e.g. for a larger payment) could have saved themselves the effort. The Lightning network, which is suitable for small, inexpensive payments, also offers a certain degree of privacy, but is not very suitable for moving millions of dollars in a single transaction.